Why you should never use Sleep Mode
Why you should never use Sleep Mode
Your data is at risk if you do not use disk encryption
If you store any confidential data on your laptop or notebook, you should really be using some form of disk encryption to help protect against data loss if the device is lost or stolen. An unencrypted disk can simply be attached as a secondary drive in an attacker controlled computer, and its data accessed directly without knowledge of the operating system login and password.
However, even if encryption is in place, your valuable data could still be at risk if you use sleep mode as the disk drive is left in an unlocked state. If somebody then has physical access to your laptop, there are a number of ways of accessing the data without knowing any passwords.
Disk Encryption options
Disk encryption is available with software or hardware based solutions. Software encryption is available from third party vendors, both commercial and open source, and is now also natively available in most operating systems. Third party software encryption options include Full Disk Encryption (FDE) or specified file / folder encryption, whilst native operating system encryption usually supports FDE only.
Hardware encryption is available with Self-Encrypting Drives (SED), and as encryption is performed by a dedicated chip on the disk, there is virtually no performance impact on the operating system as is the case with software based encryption. SEDs typically operate with the OPAL 2.0 specification defined by the Trusted Computing Group, although other operating modes exist such as Microsoft Encrypted Drive (eDrive), BIOS ATA Security (legacy), and other custom or proprietary implementations.
Full Disk Encryption (FDE) is one of the most effective ways to protect data from falling in to the wrong hands if the device is lost or stolen, as a password or similar authentication is required in order to unlock the disk before the operating system is loaded.
FDE encrypts the data at rest, which is the data stored on the hard disk, rather than in the memory of the device. Whilst the disk is in a locked state, its contents are completely unreadable, however, once the disk has been unlocked with the correct password, the data is available to anybody that has access to the device, either physically or remotely.
Shutting down the device, or even using the hibernation mode on a laptop will lock the disk and protect the data. However, using the sleep mode option does not lock the disk, and there are proven methods of gaining access to the data stored on the disk without the operating system password being known.
Bypassing Encryption passwords
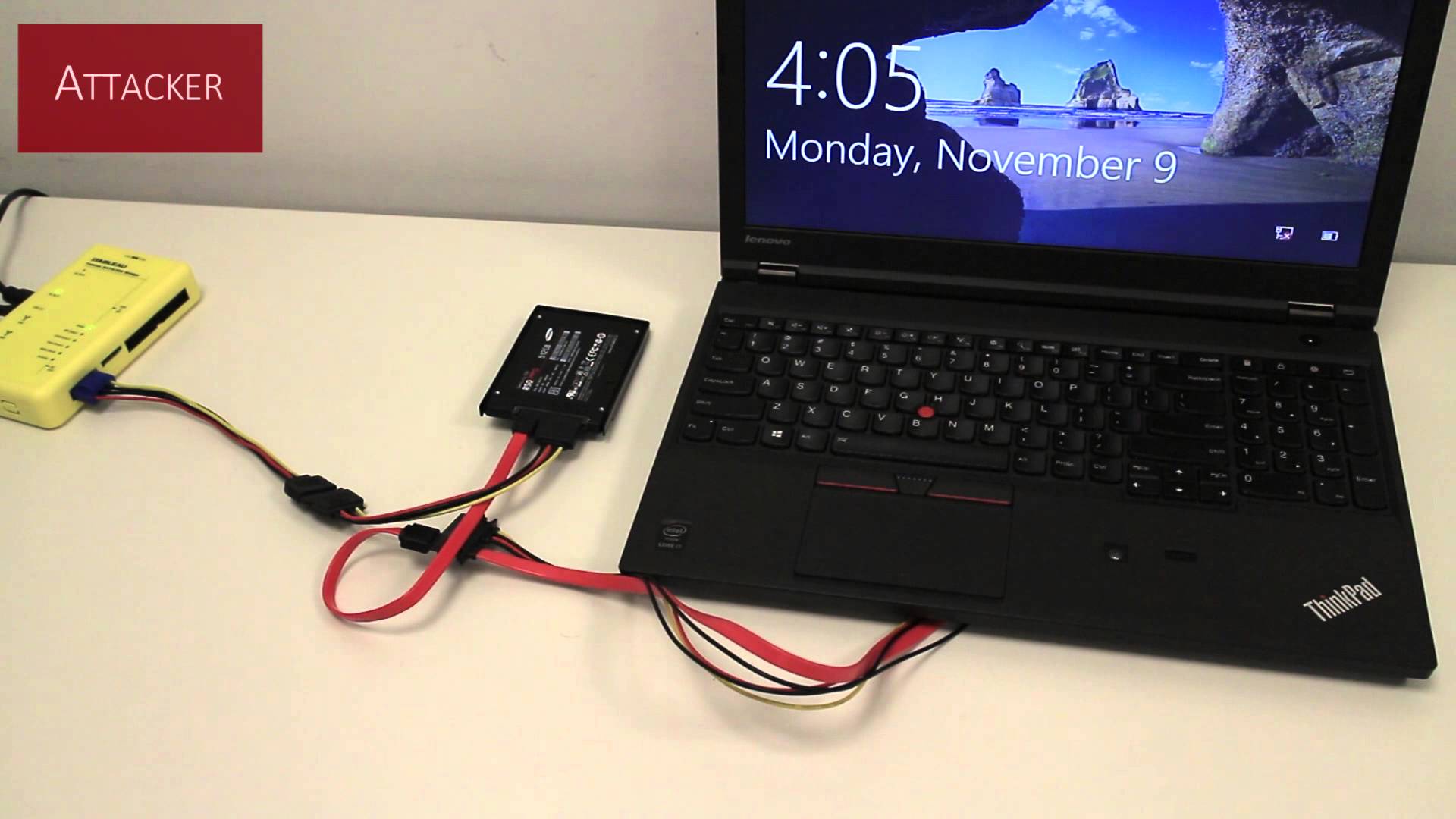
With physical access, it is possible to switch the SATA data cable from the disk to another device controlled by the attacker, either directly or by using a SATA extension cable. As power to the disk is maintained by the ‘sleeping’ device, it will remain unlocked allowing the data to be accessible on the attacker controlled device.
Some laptop models have a built-in security feature that detects when the SATA data cable is unplugged from a disk, and prevents the disk from automatically unlocking when brought out of sleep mode. However, under testing, this feature was only found to be successful with the ATA Security mode, and failed to detect the cable switch with SEDs using the OPAL and eDrive modes.
There is a similar method that involves pulling the disk out just enough to expose the SATA connections but not enough to disconnect the disk, connecting a powered SATA extension cable from another device to the disks connectors, removing the disk from the laptop and then attaching the SATA data cable from the other device to the disk to provide access to the data. This method does not require the original device to be put into sleep mode, and is therefore likely to circumvent any security features designed to detect the disk being unplugged whilst in sleep mode.
It is also possible to access the data on an unlocked disk by forcing a soft-reset of the operating system, typically by generating a crash state such as the Blue Screen of Death (BSOD) in Windows. A BSOD can be triggered using a custom USB board such as a Facedancer, and sending invalid instructions back to the operating system. It is also possible to trigger a BSOD by shorting specific pins on a memory module, although this is more often than not likely to cause hardware damage. Once a soft-reset has been triggered, the disk will remain unlocked, and it can then be booted from an alternative method such as a CD/DVD or USB to run an operating system that will allow the attacker direct access to the data on the unlocked disk.
Some laptop models with eDrive SEDs were found to be immune to the soft-reset attack method, although all OPAL based models tested were found to be vulnerable.
Recommendations
The good news is that all of these attack methods can be easily mitigated against by avoiding using the sleep mode feature, and always either shutting down the device or using the hibernation feature. The sleep mode feature can be disabled easily in Windows and other operating systems, whilst the laptop or PCs automatic sleep feature should be set to ‘never’ as well. Certain software encryption and management solutions can force sleep mode to be disabled, and are recommended where central configuration and management is utilised.
The Windows automatic restart on BSOD feature should be disabled to prevent an attacker rebooting the device from CD/DVD or USB media. This attack can also be mitigated by preventing booting from alternative sources in the BIOS configuration, and only allowing boot from the primary disk.
It is possible that SED and laptop manufacturers have developed safeguards to protect against these attack methods in future products or through firmware upgrades for existing products, however, it would still be good practice to avoid using the sleep mode feature so that the disk is locked and hiding your valuable data.
Speak to J2 Technology today about how we can help with your data encryption requirements.



